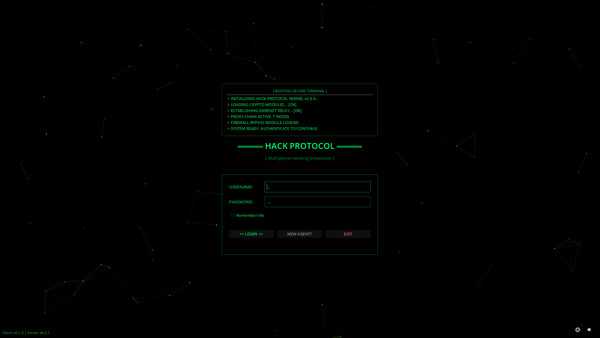
A multiplayer hacking simulation where every player runs their own server in a shared network.
Write software, crack passwords, exploit vulnerabilities, deploy viruses and cover your tracks before the FBI catches up.
YOUR OWN HACKER OS
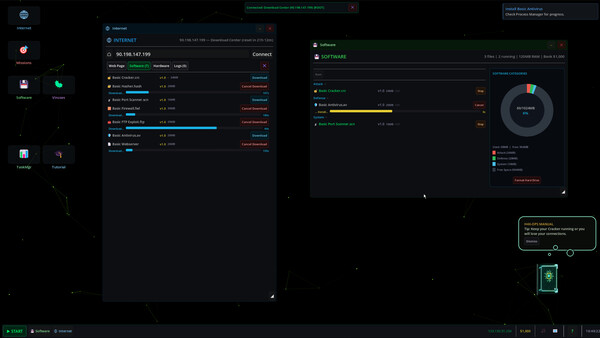
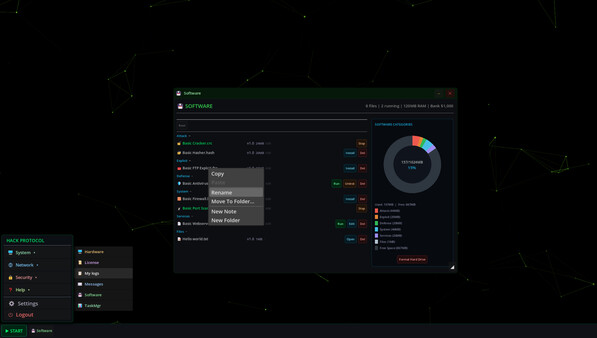
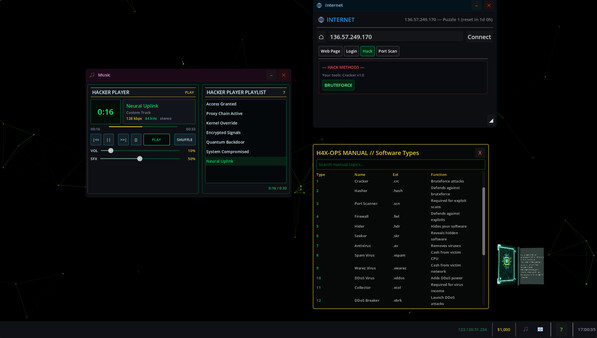
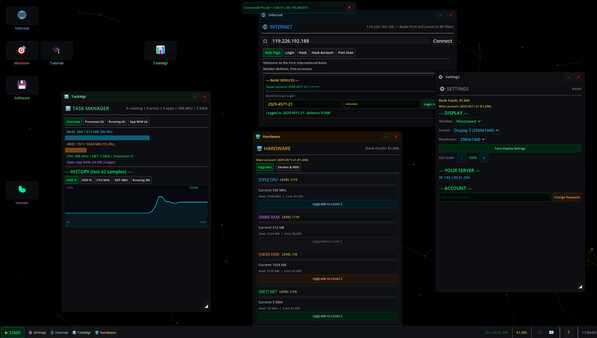
Boot into a fully functional desktop with draggable windows, a command-line terminal, and 20+ applications — from an internet browser and software manager to a virus deployer and FBI tracker. Every action plays out on your screen like a real operating system.
BUILD YOUR EMPIRE
Deploy viruses on compromised servers for passive income. Monitor your botnet through the Virus Manager. Upgrade your CPU, RAM, and network hardware. Mine Bitcoin. Accept contracts from the Mission Board. Climb the rankings.
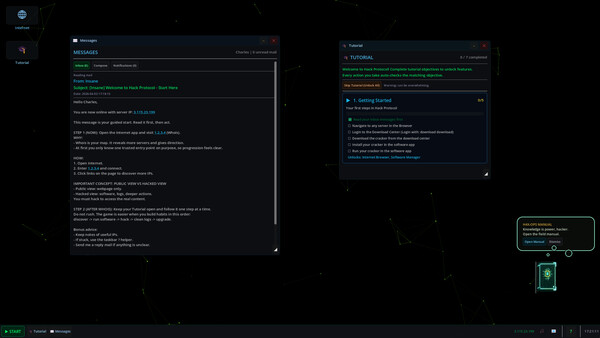
NO EXPERIENCE NEEDED
Never hacked before, not even in a game? No problem. A built-in step-by-step tutorial walks you through every mechanic, from your first server breach to deploying viruses and covering your tracks. A floating 3D Wiki Book lives on your desktop with searchable guides on every app, software type, and strategy.
Everything is explained in plain language. No real tech knowledge required.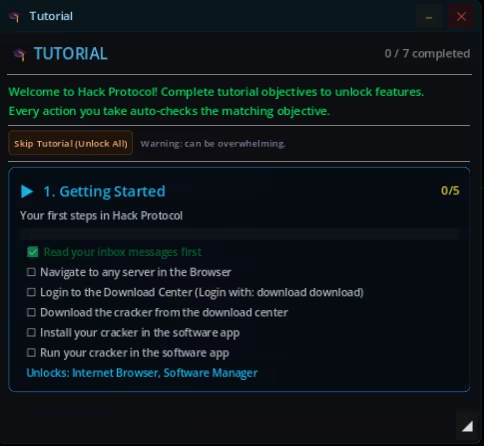
HACK EVERYTHING
Two attack paths: Bruteforce (Cracker vs Hasher) or Exploit (Port Scanner vs Firewall).
Hack NPC servers from small businesses to NSA databases, or breach real players in multiplayer.
Every hack leaves a log. Forget to delete it and the FBI builds a case against you.
17 software types across offense, defense, stealth, and chaos, each with a direct counter.
Higher versions are stronger but take longer to compile.
FBI IS WATCHING
Your wanted level ranges from CLEAR to PUBLIC ENEMY #1.
Every sloppy hack adds evidence. Delete your logs, pay your fines or wear that five-star bounty like a badge of honor.
DOOM VIRUS
Every puzzle you solve reveals the next server. Every server gets you closer to the NSA. Breach it, and you'll find the Doom Virus the most dangerous software in the game.
Survive. Spread. Make sure your name is never forgotten.
FEATURES
• Full hacker desktop OS with 20+ apps and a working terminal
• Multiplayer hack real players, global chat, live leaderboards
• 110+ NPC servers from Easy to Legendary
• 17 software types with rock-paper-scissors counters
• Virus deployment, botnet management, and DDoS attacks
• FBI wanted system with evidence tracking and bounties
• Bitcoin mining and banking with multiple accounts
• Hardware upgrades affecting real process speeds
• Puzzle trails, certifications, and mission contracts